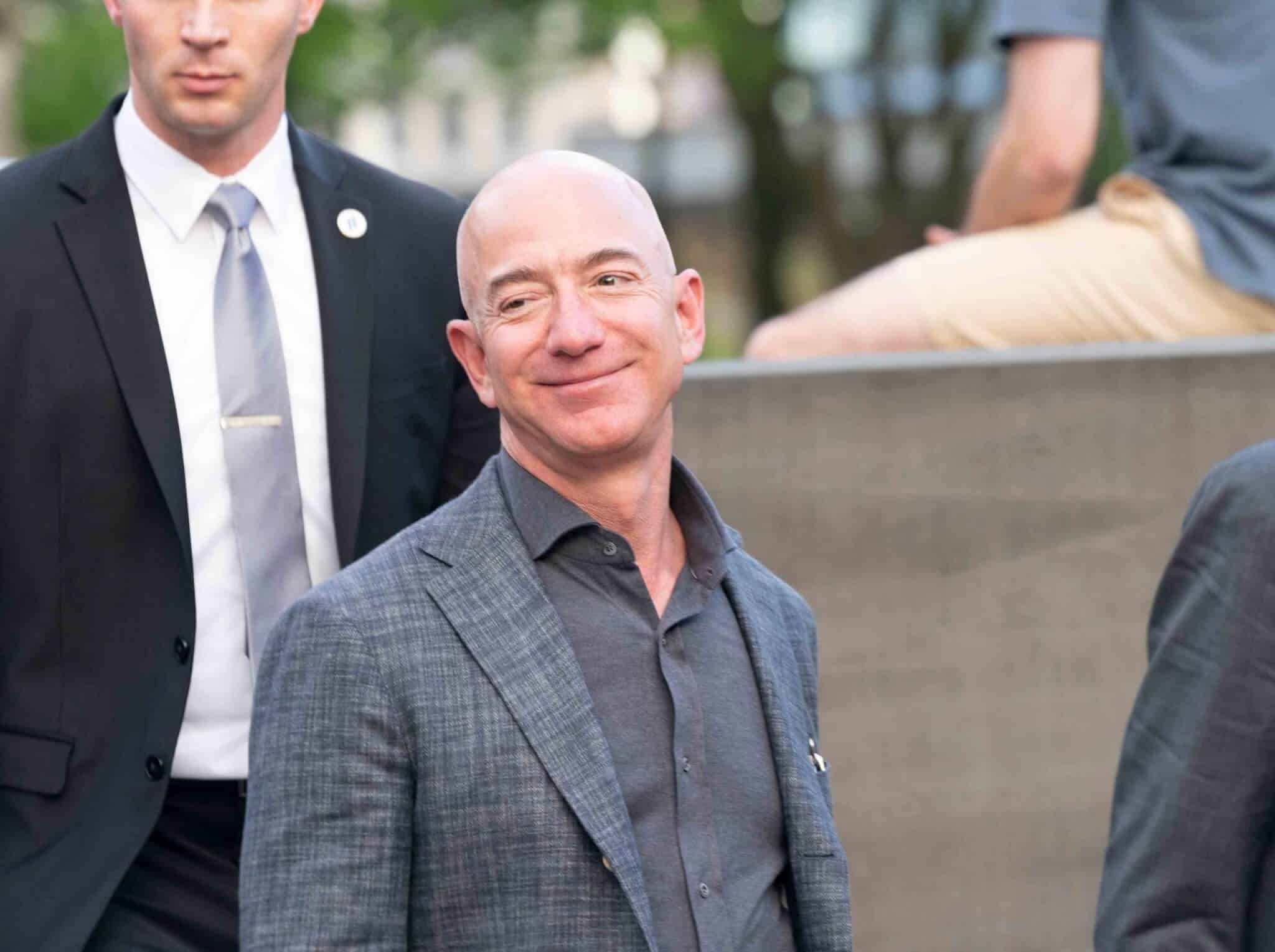
For the last several months, many of us in the mobile technology security community have heard rumors about Jeff Bezos’ iPhone. Not that he had access to a special new model or something good, but something quite bad – that his iPhone had been remotely compromised by a well-funded group to gain access to his personal information as the result of a business deal gone bad.
What is surprising about this security incident is that Bezos has access to some of the best cyber security professionals in the world. He has a dedicated team who looks after his physical and cyber protection. If this type of attack can be successful with Bezos as the target, then nearly anyone is just as vulnerable (probably more so because most don’t have the cyber protection resources Bezos does).
Business leaders rely on their mobile devices on a daily basis, and the Bezos incident won’t change that. So, what do business leaders need to know about the risks of using mobile technology, how mobile vulnerabilities can be exploited, and what organizations can do to reduce the risk of targeted mobile attacks against senior executives?
As I travel around the world for business and pleasure, it always shocks me just how long people in Europe keep their mobile devices. The number of iPhone 4’s and 5’s, and older Android devices are too many to count. Many of these people I assume to be in positions where a new phone isn’t a luxury out-of-reach, so when considering why this is, I surmise it may a combination of factors such as European frugality or with a culture of making things last for the sake of reducing environmental impact.
What I don’t think these business travelers realize is that the level of difficulty to remotely take over an iPhone 4, 5, 6 or 7 is remarkably low. For under $500, I could hire a cyber mercenary online to take over a person’s device by merely sharing the target’s phone number with the attacker. The technology to perform this attack is not secret or hidden on the dark web. It is publicly available on source code repositories like Microsoft’s GitHub. In market analysis I have been conducting in conjunction with IANS Research, I estimate 40% of US employees of major companies have devices that are vulnerable to mobile attacks and over 60% of EU employees are vulnerable. To apply that math, in most EU-based companies I would estimate that 6 out of 10 senior business leaders’ mobile devices are vulnerable to remote attack.
So what? Why should senior business leaders be concerned about these vulnerabilities? Economically-motivated attackers are looking for data these devices store. The primary target would be the target’s work email credentials. This would allow the attacker to remotely view any email stored in the target’s business inbox. Then, other work-related credentials can be captured and leveraged, including corporate VPN credentials and even company-issued multi-factor authentication tokens. I’ll be showing a demonstration of just how simple this type of attack is next month in San Francisco at the annual RSA Conference.
What should be done? There are only two mobile devices business leaders should be using, an iOS device capable of running iOS 13 (iPhone 8 and later) or a Google Pixel device capable of reliably running Android 10 with all security updates (Pixel 3 and later). If cost is a limiting factor, then the best alternative is the Android One line of devices for low-cost, but securable Android.
Once the device can be secured, it is important to focus on the applications installed on the device and how business leaders communicate with others from that device and those apps. First, let’s focus on WhatsApp, the channel through which Bezos’ phone was attacked. It is my strong recommendation that people migrate away from WhatsApp as quickly as possible. It has become a massive security vulnerability that most organizations do not have the talent nor technology to manage. Nearly any alternative is better than WhatsApp. Not only does it suffer from significant attack traffic, but Facebook is actively monetizing all of the data sent through the application. If someone absolutely needs to use WhatsApp, then I highly recommend installing it on a completely separate mobile device from the one used for work-related tasks like email and other enterprise applications.
When it comes to other applications, an ounce of prevention is better than a pound of cure. Setting strict mobile application policies which prevent the installation of free or pay-in-app games is crucial. As with anything in life, ‘free’ is never ‘free’. Most free games that people install on their phones are really just contact list monetization tools. When the application is installed and if the app is granted access to contact lists on the device, those details are harvested by the application, sent to the application developers who then monetize that data for targeted marketing and sometimes much worse. I have been asked by clients to investigate cases in which mobile contact data was harvested through a mobile game application and then used as part of a targeted cyber attack against an organization’s executives, their home computers and the devices of their family members.
The bottom line is – it’s time to pay closer attention to serious threats that mobile computing pose to businesses and the leaders of those businesses. Organizations that do not have the discipline or the right technologies to maintain strict mobile security standards and policies will suffer from either opportunistic attacks, or even worse, targeted ones which will materially impact their businesses.
Author: Aaron Turner, Board Member & Security Advisor at HighSide Inc.